Last time on our blog, we explored what made fileless ransomware so different from other malware ...
Three Effective Tips for Achieving a Sound Cybersecurity Policy
In an effort to ensure that every user is safer and more secure online, government and industry ...
Spam Traps and BlackList Domains and How They Can Affect You
In the world of email marketing, there are protections put in place to keep individuals safe fro ...
The Strong Password Paradox
Recently, a 2003 security report that was included in the National Institute of Standards and Te ...
Web Security Report Now Provided By Cloudbric
Cloudbric was created for users of all backgrounds, with all types of different websites. You mi ...
The Big Three Questions for Cloud Security
The Cloud is a cost-effective option for many businesses. Businesses can store information ...
Can Security Patches Backfire?
There are those that purport that updating your Content Management System (CMS) is one of the mo ...
What Is Fileless Ransomware?
BackgroundRansomware isn’t a new phenomenon. The concept of holding locked files for ransom ha ...
The Top 10 Hackers Arrested in 2017
Cyber criminals are rampant. Active on the dark web, hacking forums, or other platforms that fac ...
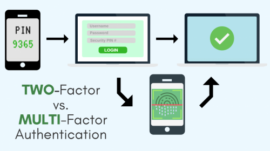
Two-Factor vs Multi-Factor Authentication
When the best online security practices are being discussed, there’s always someone that b ...